“How is your day going?” I asked my friend.
“This one friend of mine was just diagnosed with cancer,” he replied. “I’m worried about him …”
What started out as a very average conversation suddenly took a personal turn. We were out for a walk and there was nobody around; just us. With the knowledge that we were the only ones within earshot, were were able to be open and honest with each other in a way that is so necessary for our well-being as humans.
Our words were intended for each other, and nobody else. Would there be any harm in a stranger hearing our conversation? Perhaps not materially, but that isn’t the point. We needed the time alone together to sort through life.
Based on the context at hand, people tune what they share and discuss. With strangers, we talk about the weather. With our dearest loves, we expose the inner workings of our thoughts. And there’s an entire spectrum in between these extremes.
Digital communication is no different—it requires the same discretion, but too often obscures the true context. With services like Facebook, WhatsApp, Zoom, and others, privacy is always a question, and thus deserves the same treatment as a stranger. This drives the need for truly private digital communication, so we can keep in touch with people who aren’t strangers while leaving the strangers out.
This is the fundamental importance of encrypted messaging services like Signal. But can we know if Signal is trustworthy?
For starters, Signal is open-source. To many people, this is synonymous with “free of charge,” but that’s not what the term means. Open-source refers to the state of the written code itself, known as “source code.” If you say the source code is open, that means anybody can read it. This would be akin to publishing the blueprints for your garden shed: anybody can look at the drawings and see that it is a fine 2m by 3m rectangle, constructed of plywood and 2x4s, mounted on concrete footings, featuring a metal roof and a large doorway secured with a padlock.
Likewise, anybody can download and pore over Signal’s source code. This is key—security researchers, software nerds, and hobbyists alike can take a look. It’s hard to hide a dirty secret (or a malevolent code change) when the whole world has access to the source. Contrast this with a black box like Facebook: nobody but Facebook knows what goes on inside. Open software inspires increased trust because its building blocks are out in the open for all to see.
Recently, a company called Cellebrite claimed to have broken Signal’s encryption. The implications are huge, since if true, this would mean every message you send or receive would be readable by any middleman. This assertion set in motion an intriguing series of responses from both Signal and Cellebrite, which I unpack below.
After Cellebrite’s news hit the media, Signal debunked every claim they had made. Cellebrite initially made it sound like they could intercept any Signal message in transit and decrypt it. This is, importantly, entirely false. A phone must be physically plugged in to Cellebrite’s hardware and software package, which then reads out the contents. The key takeaway is this: the phone must be physically in the possession and control of somebody else, not you, for this to occur.
But there are still some nuances. If you own an iPhone, and power it off, everything on it is encrypted until you unlock it the first time. While unlocked, everything is decrypted and readable. Once you lock it again, many things (but not everything) are once again locked away. This is likely done to save energy and time, and to allow the device to connect to Wi-Fi, receive emails, and do other such tasks while locked. If you unlock your phone and hand it to somebody, they can obviously read through all your messages, look at your photos, read your mail, etc. This is exactly what Cellebrite does—using their fancy hardwired connection, they can download unencrypted contents off your device and save it, including your Signal conversations. Is this a risk? Just power off your phone before you hand it to somebody you don’t trust, and its contents will remain encrypted. If your passcode is long and strong enough, they will spend forever attempting to stumble on the correct code.
At this point I thought the story was over. But just this week, Signal founder Moxie Marlinspike announced that he had acquired a copy of Cellebrite’s hardware and software. As a software developer and security researcher himself, he found basic security flaws inside Cellebrite’s own software, allowing him to use specially formatted files to control the attacking computer attempting to crack a device. Allegedly the software could be commanded to do anything from displaying a popup, to modifying any or all of the logs from previously-cracked devices stored on the computer, or even altering logs from devices cracked later. Clearly this makes the software useless as a forensic tool.
Choosing a service to trust is difficult. How do you know who just talks the talk, and walks the walk? It’s hard to beat a critically acclaimed open-source app designed firstly for security and privacy in messaging. Signal issued a bold rebuttal to the false claims that Signal’s encryption had been broken. And its founder has advanced his reputation by exposing critical vulnerabilities in the flagship software sold by the very company which made those false claims.
Signal walks and quacks like a trustworthy duck. Join me on Signal!

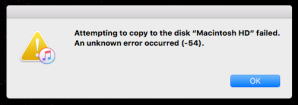

 Settings” nervously, considering the implications, when I decided to have one more crack at the Internet. Down in the depths of a comment section, a helpful
Settings” nervously, considering the implications, when I decided to have one more crack at the Internet. Down in the depths of a comment section, a helpful